Trust Center
Security, compliance, and data protection information for Votazz products.
Compliance & Certifications
Votazz meets industry-standard security and compliance requirements.
Atlassian Security Review
Every Votazz app is independently reviewed by Atlassian Marketplace staff and passes automated Ecoscanner security scans on every release. We follow Atlassian’s Security Bug Fix Policy for vulnerability remediation.
Learn More →Legal Documents
End User License Agreement
EULA per app is available on the Atlassian Marketplace listing.
View on Marketplace →Our Products
Data Center Apps
Our Jira and Bitbucket Data Center apps are built on the Atlassian Plugins2 framework. All apps undergo Atlassian technical review and security scanning on every release.
Data handling: DC apps run inside your Atlassian instance. Votazz has no access to your data unless you explicitly request support.
Browse DC Apps →Cloud Apps (Forge)
Our Cloud apps are built on Atlassian Forge — they run on Atlassian’s secure infrastructure, not on our servers. This means AES-256 encryption, TLS 1.2+, AWS Lambda isolation, and automatic data residency.
Your data stays with Atlassian. No data leaves the Atlassian ecosystem without your explicit permission.
Learn about Forge Security →Performance & Scale Testing
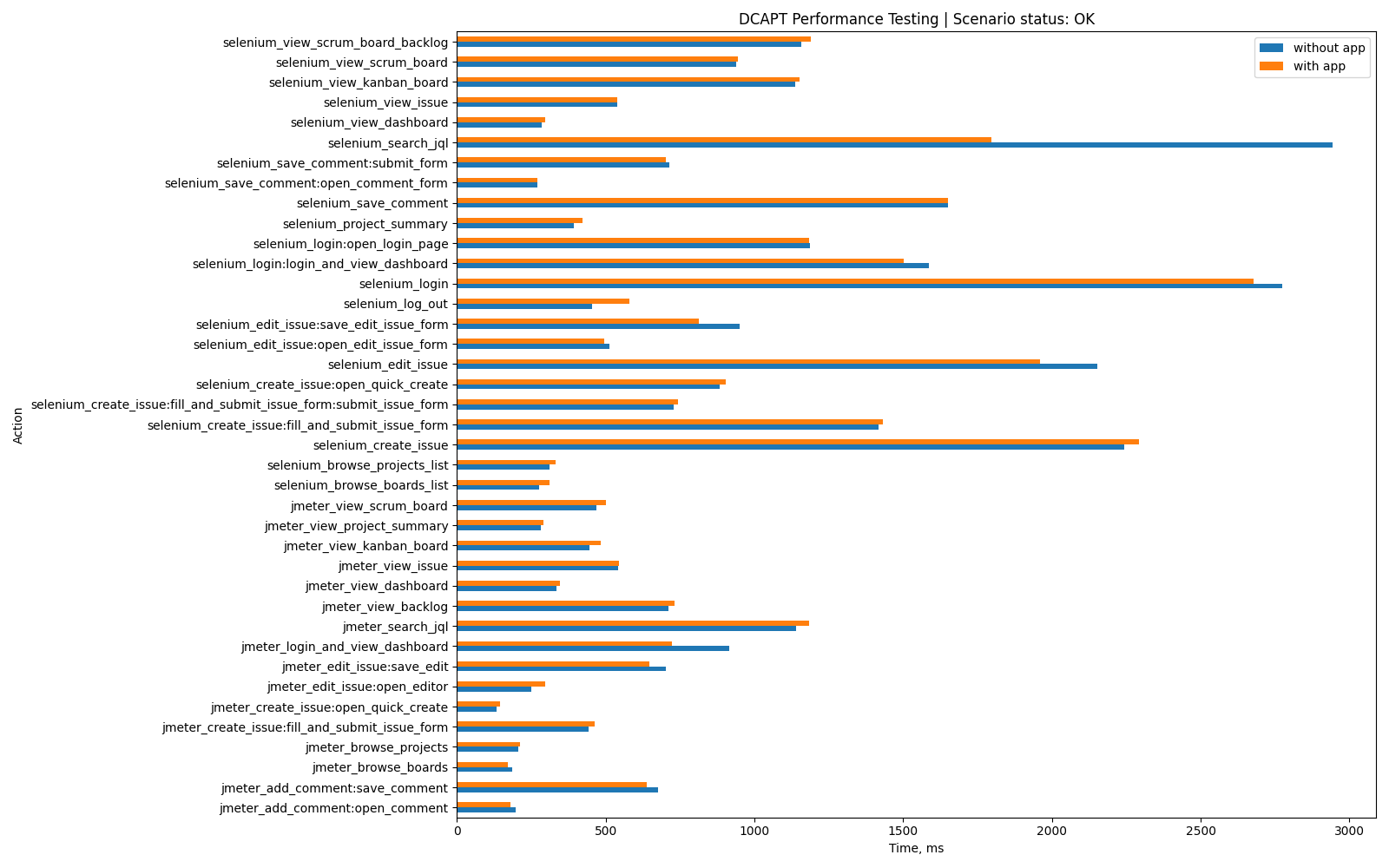
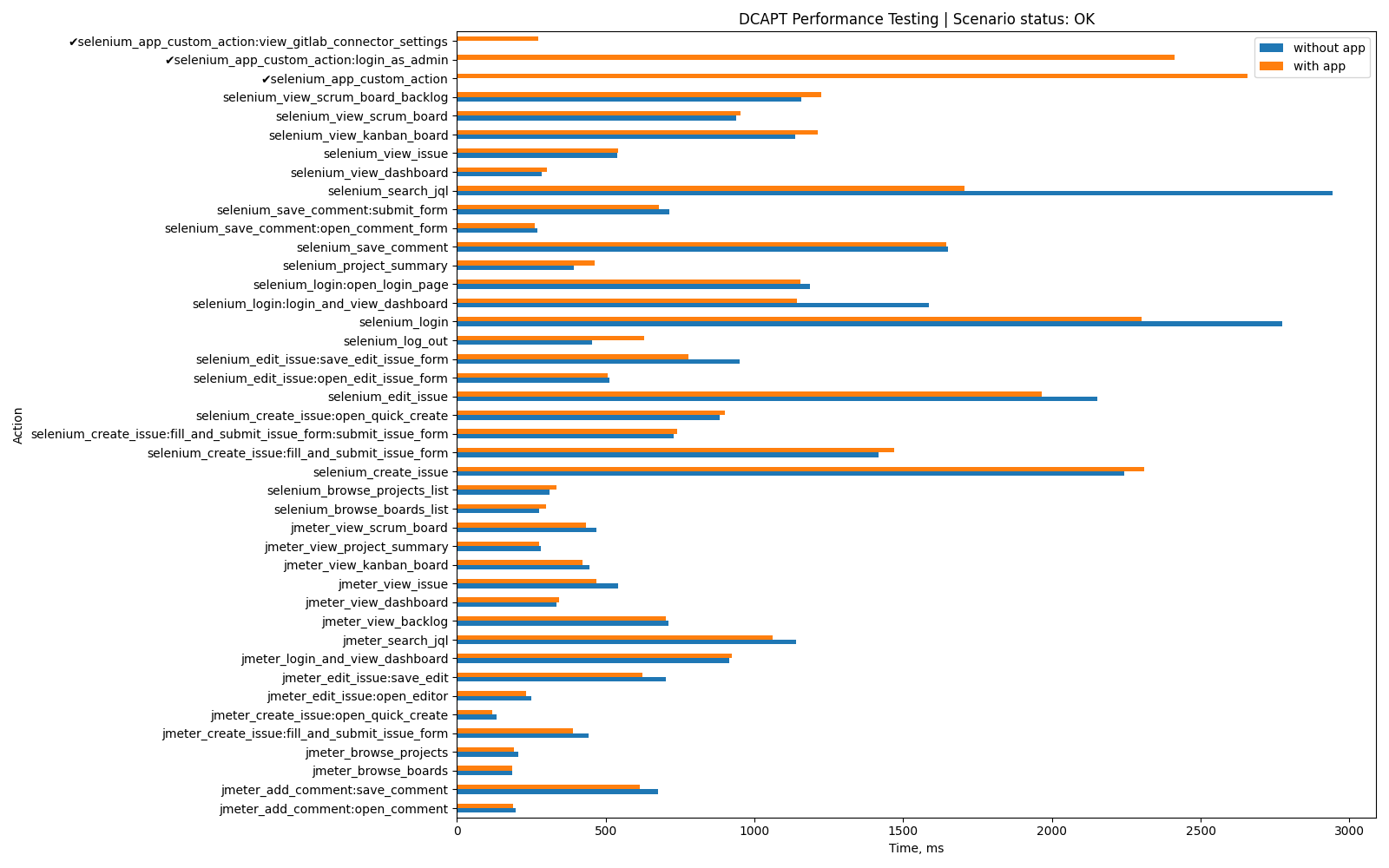
All Votazz Data Center apps are tested using the Atlassian DC App Performance Toolkit.
Test environment: Jira Data Center 11.3.1 · 200 concurrent users · 1,053,396+ issues dataset · 100% success rate
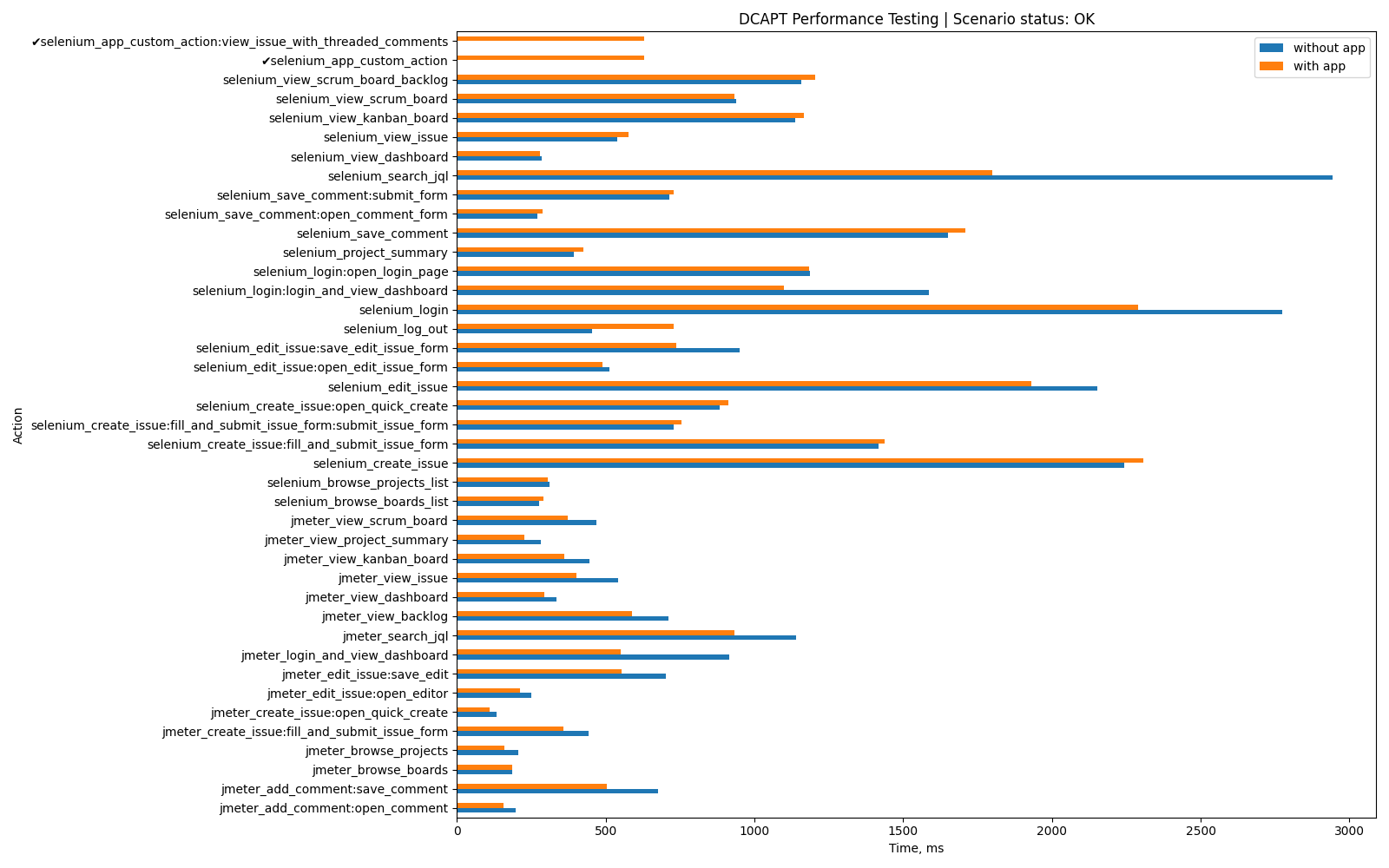
Threaded Comments for Jira
DCAPT Compliant · 0% overhead on core Jira actions
Download Full Report →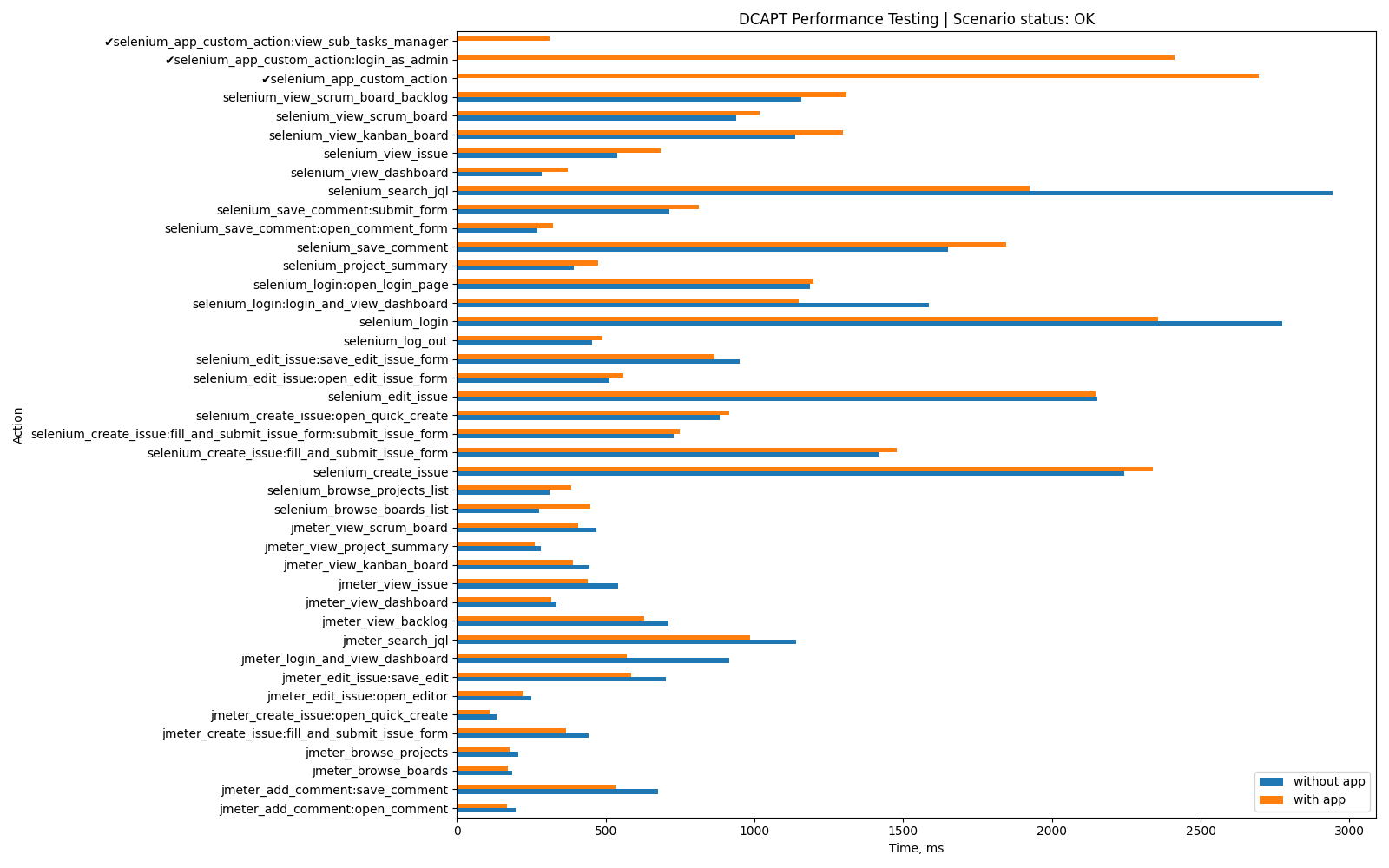
Sub-tasks Manager for Jira
DCAPT Compliant · All actions <1s at 90th percentile
Download Full Report →Encryption & Data Protection
Cloud (Forge) apps
Forge apps run on Atlassian’s managed infrastructure. Data is encrypted at rest with AES-256 and in transit with TLS 1.2+. Encryption keys are managed via AWS KMS. Data residency follows your Atlassian Cloud site settings automatically.
Data Center apps
All plugin settings that contain secrets (API tokens, webhook URLs, passwords) are encrypted using Jira’s built-in EncryptionService. Nothing sensitive is stored in plain text in your Jira database.
Web properties (votazz.co, docs.votazz.co)
All Votazz websites use TLS 1.3 with certificates auto-renewed via Let’s Encrypt / Cloudflare. HSTS (HTTP Strict Transport Security) is enabled on all production domains. All web traffic is HTTPS-only.
Data Retention & Deletion
Votazz apps are designed so your data stays where it already lives. We do not store customer production data on our own infrastructure.
Data Center apps
All data stays inside your self-hosted Jira instance database. Votazz has no copy, no backup, no access.
Cloud (Forge) apps
All data stays on Atlassian’s infrastructure under your Atlassian Cloud site. Votazz has no external copy.
What we actually store on our side
Only what’s needed to operate the business: license and billing information received from Atlassian Marketplace (handled by Atlassian), support emails you send us, and anonymous aggregate install statistics via Atlassian analytics. No production customer data, ever.
Uninstalling an app
When you uninstall a Votazz app, its configuration is removed from your Jira instance (for DC) or from Atlassian storage (for Cloud). There is nothing for Votazz to delete on our side because we do not have a copy.
GDPR right to erasure: if you want your billing or support contact data removed, email support@votazz.co. We process such requests within 30 days as required by GDPR.
Secure Development Practices
Every line of code that reaches production goes through automated checks, review, and testing before release.
Pull request workflow
No direct pushes to production branches. Every change goes through a pull request with automated CI checks and explicit review before merge.
Automated testing
Unit tests, integration tests, and TypeScript / type checks run on every commit. Failing tests block the merge.
Dependency scanning
GitHub Dependabot monitors every dependency daily and opens automated PRs for security patches in vulnerable packages.
Secret scanning
GitHub Secret Scanning runs on every push and blocks commits that contain detected credentials. Pre-commit hooks catch secrets locally before they leave the developer machine.
Static analysis (SAST)
CodeQL analyses code for security vulnerabilities on every pull request and on a weekly schedule.
Signed commits
All commits to Votazz repositories are GPG-signed and verified, so every change is attributable to an authorised contributor.
Atlassian Ecoscanner
Every release is additionally scanned by Atlassian’s Ecoscanner platform for ongoing security monitoring of all published apps.
Linting & code quality
Automated linting and strict type-checking are enforced on every pull request. Code quality gates block merges on regressions.
Access Control
Multi-factor authentication
MFA is required on all critical services: GitHub, AWS, Atlassian, Google Workspace, domain registrar, hosting providers, and payment processors. Hardware security keys (FIDO2/U2F) protect the highest-risk accounts.
Least-privilege access
Every account and service is granted the minimum permissions needed to do its job. Production access is scoped more narrowly than development access.
Quarterly access review
Access across all platforms is audited quarterly. Stale accounts, unused service tokens, and leftover permissions are removed.
Contractor NDAs
Any contractor or consultant working on Votazz code or data signs a non-disclosure agreement before receiving any access.
Offboarding
When someone leaves the team, all access (GitHub, cloud providers, Atlassian, domain, password manager) is revoked within 24 hours, following a documented offboarding checklist.
Password management
Credentials are stored in a dedicated password manager with a strong master password and hardware-key second factor. Production secrets never leave secret-management systems.
Team & Workstation Security
Votazz is intentionally a small, focused team. Core workstation and team security practices:
- Full-disk encryption — all work laptops run FileVault (macOS) or equivalent full-disk encryption.
- Hardware security keys — physical FIDO2/U2F keys protect high-value accounts (GitHub, AWS, domain registrar).
- Password manager — unique, strong credentials generated and stored in a dedicated password manager with hardware-key 2FA on the vault.
- Separation of environments — production access requires separate credentials from development, and is approved explicitly before every privileged action.
- Automatic OS updates — security updates are applied on all workstations within days of release.
- Onboarding & training — any new team member must complete security awareness training, sign a confidentiality agreement, and use an encrypted laptop before touching production.
Incident Response & Security Contact
If you discover a security issue or believe your data has been affected, contact us immediately. We acknowledge reports within 48 hours and follow the Atlassian Marketplace Security Bug Fix Policy for remediation timelines.
Breach notification commitment: In case of a confirmed data breach affecting customer data, we will notify affected customers within 72 hours, as required by GDPR.
Contact Security TeamOur incident response playbook
We follow a structured, documented process for every security or operational incident:
Detect → Triage → Contain → Eradicate → Recover → Post-mortem
Severity levels:
- P0 (Critical) — confirmed data breach, production outage, or active exploit. Acknowledged within 4 hours.
- P1 (High) — core functionality broken for many users, unverified security report. Acknowledged within 24 hours.
- P2 (Medium) — degraded experience, workarounds exist. Acknowledged within 2 business days.
- P3 (Low) — cosmetic or minor issue. Tracked in our backlog.
Communication: affected customers are notified by email. For P0 and P1 incidents we publish a post-mortem within 14 days of resolution, describing what happened, root cause, impact, and corrective actions.
Vulnerability Disclosure Policy
We welcome reports from security researchers and invite good-faith testing of Votazz products.
How to report
If you discover a security vulnerability in any Votazz product, please report it responsibly to support@votazz.co with SECURITY in the subject line.
Include as much detail as you can: affected product and version, reproduction steps, impact assessment, and any proof-of-concept code. Please do not publicly disclose the issue until we have had a reasonable opportunity to investigate and fix it.
Scope
- All Votazz apps published on the Atlassian Marketplace (Jira Data Center and Cloud, Bitbucket Data Center and Cloud)
- votazz.co and its subdomains (docs.votazz.co, etc.)
- Any publicly accessible Votazz production API or webhook
Out of scope
- Denial-of-service (DoS) attacks or load testing
- Social engineering of Votazz staff, partners, or customers
- Physical access or theft of devices
- Automated scanner output without manual verification and an exploitation path
- Issues in third-party services Votazz integrates with but does not control (e.g. the underlying Atlassian platform)
- Missing best-practice headers (e.g. CSP report-only) without a demonstrated impact
What we commit to
- Acknowledge your report within 48 hours
- Keep you updated on triage and remediation progress
- Credit you in our security acknowledgements with your consent
- Not pursue or support legal action against good-faith researchers who follow this policy
- Remediate confirmed issues according to the Atlassian Marketplace Security Bug Fix Policy (Critical within 30 days, High within 90 days)
Safe harbour
Research conducted in good faith and in accordance with this policy is authorised and will not result in legal action from Votazz. We ask that you only test against accounts you own, minimise data exposure, and do not exfiltrate or retain customer data.
Frequently Asked Questions
Where is my data stored?
For Data Center apps: data stays within your self-hosted Atlassian instance. Votazz never receives or stores your production data.
For Cloud (Forge) apps: data is stored on Atlassian’s infrastructure with automatic data residency based on your Atlassian Cloud settings.
Who are your subprocessors?
Votazz uses minimal third-party services:
• Atlassian Marketplace — license management, customer contact
• Google Workspace — internal email and support ticketing
• AWS (via Atlassian Forge for Cloud apps)
A full subprocessors list is available on request in the DPA.
What is your vulnerability disclosure process?
Report security vulnerabilities by emailing support@votazz.co with “SECURITY” in the subject line. We acknowledge reports within 48 hours and follow the Atlassian Marketplace security bug fix SLAs for remediation.
Have you been independently audited?
Yes. All Votazz Data Center apps pass Atlassian Marketplace technical review and security scanning on every release. We are SOC 2 Type II audited — the full report is available on request for enterprise customers.